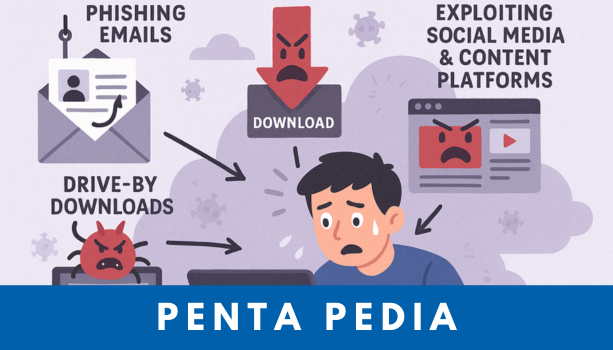
InfoStealer: The Silent Cyber Threat Lurking in Your Digital Life In the age of digital […]
Read moreCurrently browsing: Blog
[Security News] Pandora, Chanel and more Suffers from Data Breach
6th August 2025 Pandora Suffers from Data Breach After Data Theft Attacks Pandora, the Danish […]
Read more[Security Issue] Digital Transformation in Southeast Asia and the Middle East
Digital Transformation in Southeast Asia How is Southeast Asia and the Middle East Handling […]
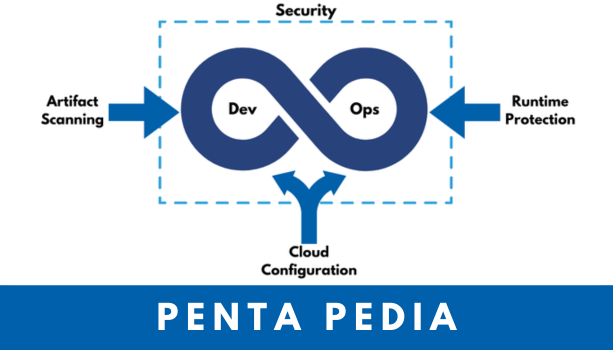
Read more[Penta Pedia] What is CNAPP? And How to Secure Cloud Environments?
CNAPP: the All-in-One Cloud Security Platform for Modern Enterprises Creation of CNAPP: […]
Read more[Penta News] Data Encryption Solution D.AMO Has Operated Normally for Over 17 Years
“At Penta Security, our encryption solution D.AMO and WAAP platform WAPPLES have maintained the #1 […]
Read more[Security News] French Telecom Orange Hit by Cyberattack
30th July 2025 French Telecom Orange Hit by Cyberattack Orange, a French telecommunications company, […]
Read more[Penta Inside] The 28th Anniversary of Penta Security
Penta Security Celebrates 28 Years of Innovation in Global Cybersecurity July is both […]
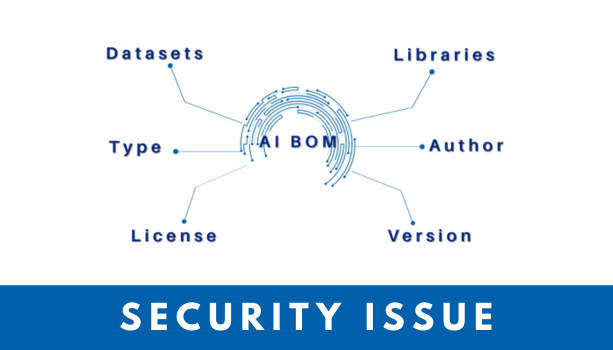
Read more[Security Issue] AI BOM: Enhancing Transparency and Trust in the Age of Artificial Intelligence
What is Artificial Intelligence Bill of Materials (AI BOM) and why do we need it? […]
Read more[Security Issue] Hackers Now Use AI: Evolving Cyber Attacks and Emerging AI Security Threats
In 2024, a finance officer at a multinational company in Hong Kong transferred the equivalent […]
Read more[Security News] Microsoft Confirms China link to SharePoint ‘ToolShell’ Vulnerabilities
23rd July 2025 Microsoft confirms China link to SharePoint ‘ToolShell’ Vulnerabilities Multiple Chinese state-sponsored […]
Read more