IoT Security
Penta Security’s IoT Security Solutions
IoT, the Internet of Things
Internet of Things. It’s likely that no other terminology in IT is misinterpreted as much as this particular one.
There’s an abundance of talk about refrigerators and lights controlled by smartphones, and understandably so, as it’s a concept that’s easier to comprehend.
However, IoT technology does need to be discussed within its full potential. IoT, or the Internet of Things, is technology where “things” or devices can
connect to the Internet and analyze information, which is consequently used as a platform for different services that users can utilize.
What is IoT security?
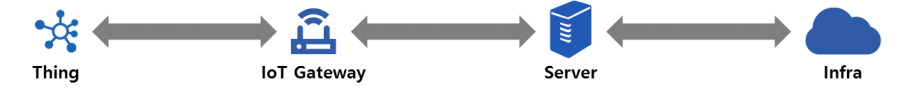
IoT Security, based upon the IoT system, can hence be divided up into four categories.
- Securing devices that collect user information.
- Securing the IoT gateways that collect the information being sent to a server
- Securing the servers to ensure the integrity of data that has been collected
- Securing the infrastructure that is the base of all these systems
Penta Security IoT Solutions
The following solutions are based on Penta Security’s core technologies: Encryption, Network Security, Authentication, and Security Services.
