Smart Product Authentication
Prevent damages caused by counterfeit products with D’EAL
Why Secure Product Authentication Matters
Per the IACC Report, counterfeit products distributed in 2012 have been valued around USD 200~600 billion to maximum USD 1 trillion, which is a 10,000% increase within the last 20 years. Products include expensive shoes, bags and jewelry as well as many medicines and auto parts, posing serious threats to people’s lives.
D’EAL is a genuine product authentication solution designed to prevent damages caused by counterfeit products using PKI-based technology and hardware duplication protection. The solution ensures the highest level of security by incorporating PKI technology into a range of areas including e-Business security solutions, public certification and end-to-end encryption, while taking advantage of our extensive expertise in this field. It supports various methods based on wireless communication technologies such as electronic tags (in the form of stickers), insertion into inner fabrics and metallic logos without compromising the brand design, while ensuring a high level of security.
By introducing this authentication solution, companies can protect their financial wellbeing and brand image, as well as their customers, from counterfeit products while improving their brand values.
Conventional Counterfeit Prevention
Several technologies have been developed for the prevention of counterfeit products, including holograms, security ink, QR codes and RFID, but all of these are limited in terms of effectiveness as they have a poor level of security and identifiability, as well as a lack of compatibility with other IT applications.
Low Security – Easy to reproduce and forge
Low Identifiability – Hard to distinguish for an average user
Low Extendibility – Difficult to apply to other use cases
Solution Features
With PKI technology and wireless communication support, D’EAL offers a user-friendly GUI and effortless compatibility with other management systems, while standing out in the following areas:
Security
D’EAL solves the limitations of existing anti-counterfeit and duplication solutions using PKI and hardware technology that do not allow duplication. The hardware copy protection technology prevents tag duplication and improves security by linking with close range communication technologies, such as PKI, RFID, NFC and beacon.
Identifiability
D’EAL can be linked to a smartphone which makes it easy to identify counterfeit products. You can authenticate products within five seconds by holding your smart phone to an electronic tag without any additional operation. It provides a secure data management system by incorporating authentication and encryption services.
Extendibility
D’EAL provides extra features such as distribution and inventory management based on close-range communication technology. By coordinating with beacon technology, it can help identify stolen items and those not for sale while preventing theft from stores through validation. If any abnormal activities are identified via data analysis, all relevant certificates are removed for security.
Diversity
D’EAL supports various types of electronic tags. Wireless communication technology can be used with a wide range of materials due to its interchangeable construction, as it can be used as a sticker, metal logo or inserted into inner fabric to maintain the original brand design and minimize any additional process for authentication.
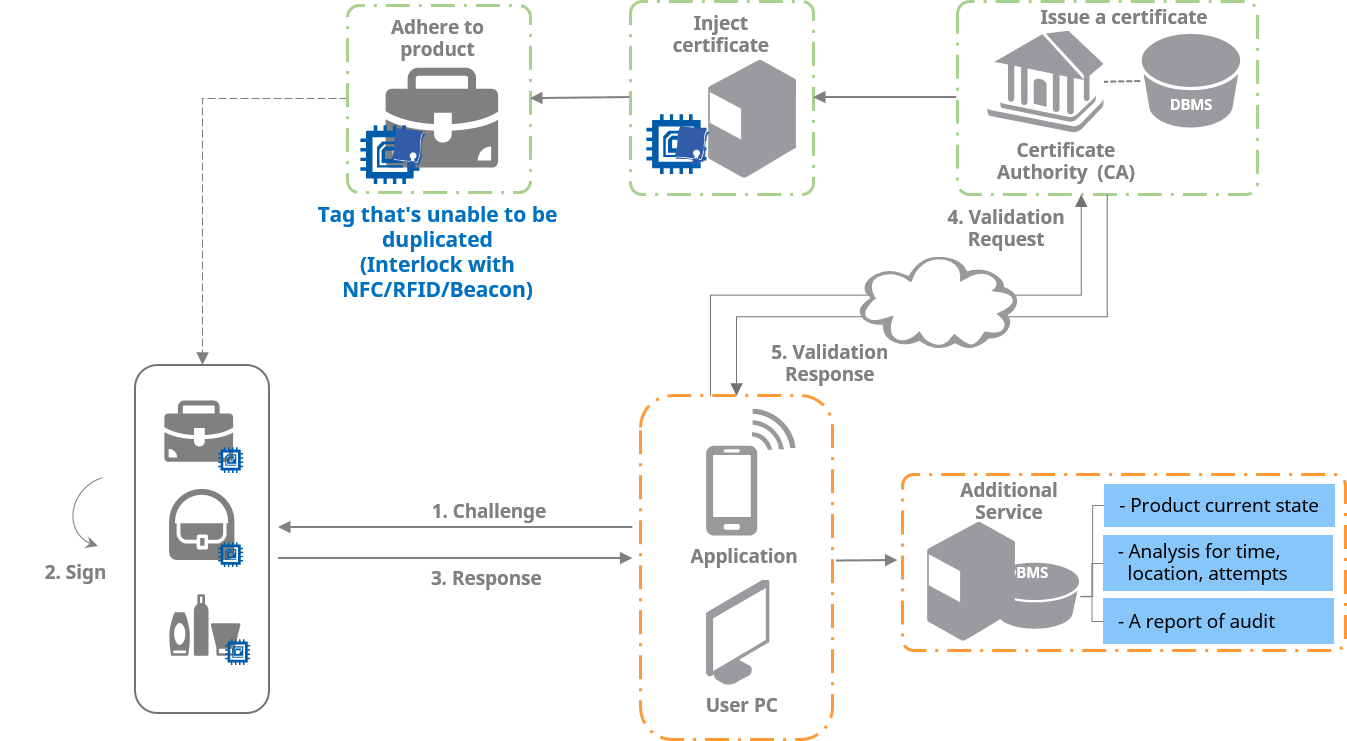
How it works: Flow Chart
Insert certificates which cannot be duplicated for authentication. Then, authenticate each tag signature using the Challenge & Response system and validate the identification data. Following these two steps, you can further improve security.
Want to learn more?
IoT brings a whole new world of possibilities. While smart factories can mean drastic savings in operational expenses and remote monitoring, IoT future does come at a price. Like all IoT applications, security needs to be assessed and implemented before any connections are made, in order to make all the convenience not simply possible – but secure.
