WAPPLES
Intelligent Web Application and API Protection
WAPPLES is a Web Application and API Protection solution (WAAP) that utilizes logical analysis to protect web applications, APIs, and mobile apps from cyber attacks.
As a market share leader in Asia-Pacific, WAPPLES is an effective solution against sensitive data exposure, website defacement, API schema protection, malicious bots, and DoS, helping organizations exceed regulatory compliance.
Powered by a logical COCEP™ engine, WAPPLES reponds newest threats, including attacks in Advanced Persistent Threats (APT) launched by malicious groups to thieve data assets of governmental organizations or enterprises. The Lower false-positive rate, based on the intelligent logical COCEP™ detection engine, of Penta Security’s WAAP solutions including Cloud based one is recognized by Gartner in 2023 market guide.

Intelligence Allows Top Performance
While traditional WAFs depend on high-maintenance signature updates for low-accuracy pattern-matching, WAPPLES uses a logic-based detection engine called COCEP™ (Contents Classification and Evaluation Processing).
Utilizing 39 pre-configured detection rules, modified and even unknown attacks are categorized and blocked heuristically and semantically. This proprietary technology allows WAPPLES to deliver superior security with industry-leading accuracy and low false positive rates under various network environments.
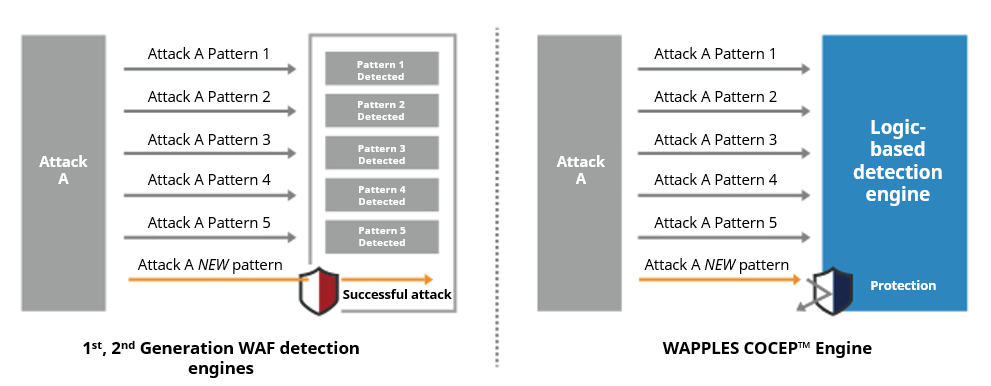
Through the analysis of an attack’s characteristics, WAPPLES is able to identify attacks that utilize new patterns of exploit that often bypass typical WAFs utilizing signature-based detection engines.
1st and 2nd generation WAFs that operate on blacklists and whitelists lag behind due to their reliance on signature updates to detect the latest threats. In comparison, the sophistication of security that WAPPLES can provide greatly surpasses that of signature-based WAFs.
WAPPLES Product Family and Related Services
Features
Appliance-type WAAP Solution
· Logic-analysis based COCEP™ engine protects websites against various cyber threats including OWASP Top 10 and API Security Risks
· Extremely low false-positive rates through heuristic and semantic traffic analysis
· Utilizes 39 detection rules that can be fine-tuned to create robust custom security policies
· Defense from known, zero-day, and HTTP DoS attacks
· Validity testing (Luhn: ISO/IEC7812) prevents leakage of sensitive data
Easy to Install & Configure
· Minimal changes to existing systems
· Quick setup with pre-configured security policies
· Statistics visualized on a centralized dashboard
· Intuitive and easy-to-use GUI management console
· Increases efficiency in web security management
Supports Various Environments
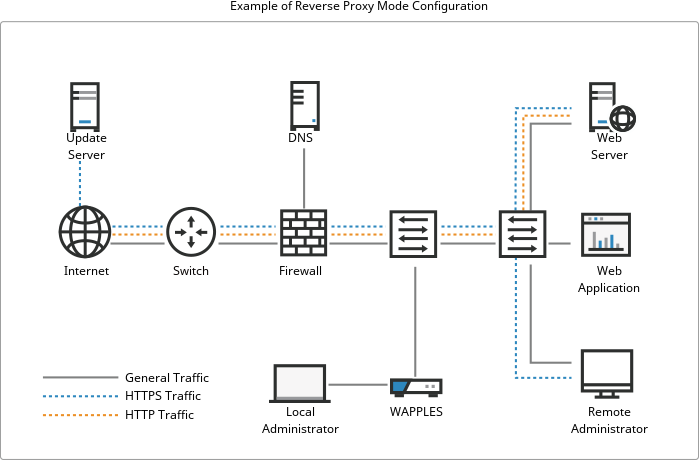
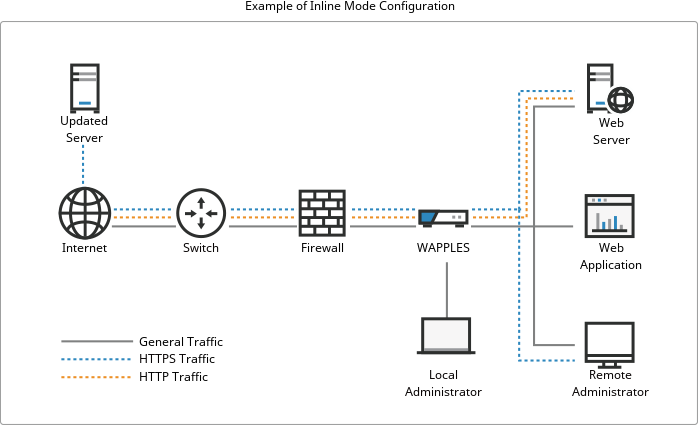
· Can be deployed in Reverse proxy, Inline, or High Availability (HA) configuration modes
· Support for EtherChannel and Multi-Segment
· Integration with SIEM
High Performance and Stability
· Optimized core provides enhanced performance
· High processing power with in-memory computing capability
· Stable performance even with strict security policy settings enabled
· Increased bandwidth through bonding technology
Deployment
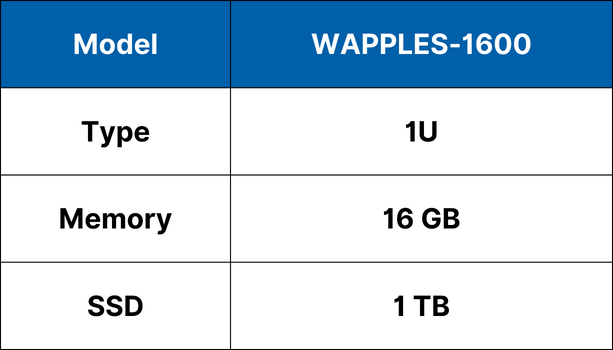
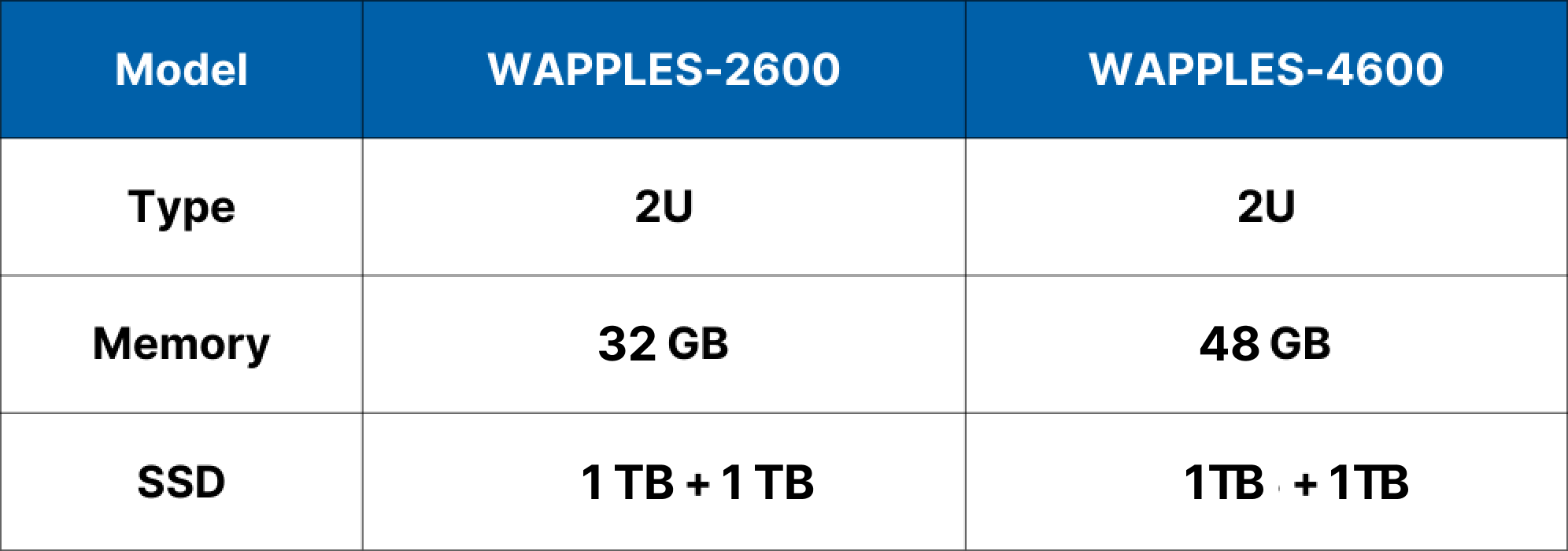
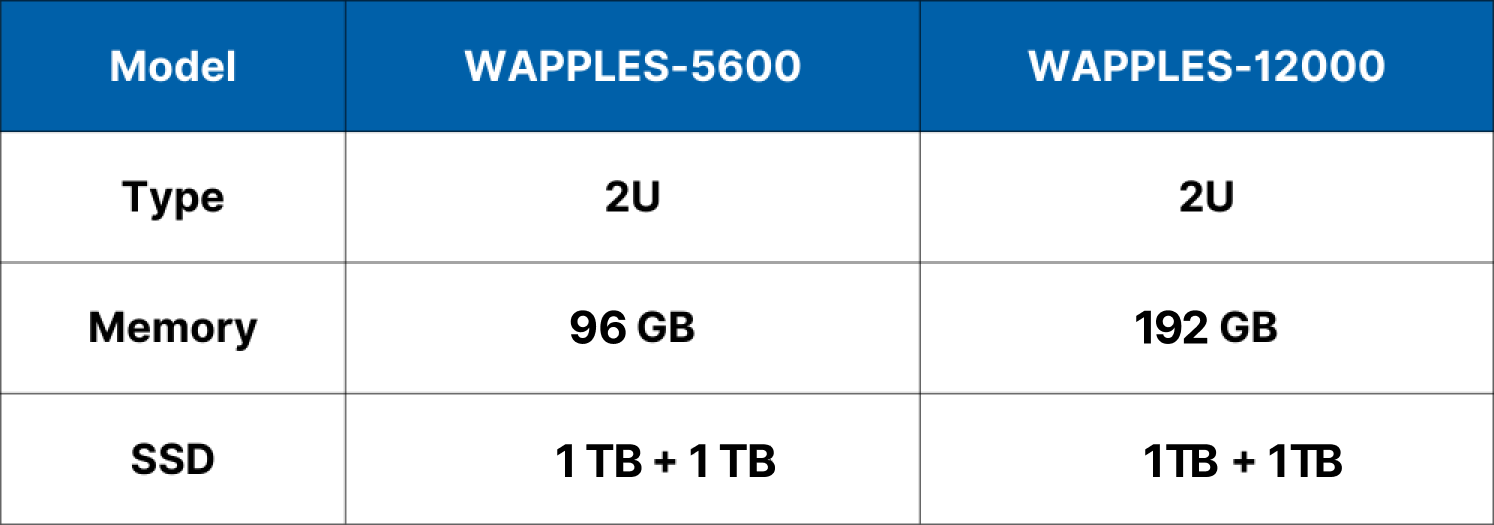
Specifications
Economy
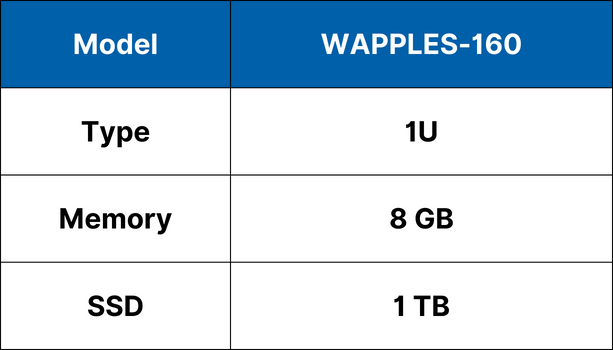
Value
Performance
High-End
*Specifications subject to change without notice.
Implementation
When a customer chooses to deploy WAPPLES, a thorough analysis of the customer environment will be conducted prior to installation. This is important for optimizing policy settings tailored to specific operational and business needs to achieve an optimal configuration. Post-installation, detection logs are also monitored over a period of time and analyzed to further fine-tune the security policies and complete the implementation process.
- Pre-Inspection
- Pre-inspection
- Install and Configuration
- WAPPLES installation
- WAPPLES configuration
- Operation testing and demonstration
- Supplement Policy
- Detection log analysis
- Analysis report
- Policy modification
FAQs
Is a web application firewall really necessary?
Yes, it’s essential if your web server contains important content, data, or personal information.
What makes WAPPLES better than other web application firewalls?
WAPPLES is an intelligent web application firewall with a machine learning-based detection engine. It blocks even unknown attacks and guarantees a low false positive rate through accurate detection. Through continuously updated detection rules and user-configurable custom rules, it analyzes and detects web attacks by type to safely protect servers from web threats. It includes four security solutions: web attack response, information leak prevention, unauthorized access prevention, and web defacement prevention, and can quickly respond to emerging attacks including the growing APT attacks. Beyond HTTP and HTTPS, it supports HTTP/2 and delivers high performance through optimized attack detection policies. Excellent Layer 4 load balancing and Layer 7 sticky session features enable stable traffic handling. The self-diagnosis feature monitors status in real time, automatically restoring service or alerting administrators when issues occur. The web GUI-based management tool enables easy security configuration across all browsers.
If WAPPLES fails, does the web service stop too?
Hardware-based web application firewalls don’t affect web servers at all and provide safe, fast detection against web attacks. In contrast, software firewalls installed on servers can slow down the web service itself and may cause false positives due to detection overhead.
What makes hardware-based web application firewalls better than software firewalls?
Software firewalls installed on servers add load to the server, which can slow down the web service and cause false positives from detection overhead. Hardware-based web application firewalls, however, don’t affect the web server at all and provide safe, fast detection against web attacks.
Will there be performance degradation when deploying a web application firewall?
While some slowdown may occur, web application firewalls actually remove garbage traffic (20% of total traffic) that burdens web servers before it reaches them, preserving web server resources. In actual customer use, you may even experience faster speeds.
