[Penta Pedia] OWASP Top 10 2025 Prediction
OWASP Top 10 2025 Prediction
Origins and Purpose of OWASP Top 10
The Open Worldwide Application Security Project (OWASP) is a nonprofit educational charity dedicated to improving software security, playing a pivotal role in web application security. Since 2003, OWASP has produced the OWASP Top 10 project to help organizations and developers initiate secure software development.
The OWASP Top 10 is built on consensus among global security professionals and functions as a standard awareness document for web application security risks. While it is not a legally binding standard or certification, it is widely adopted as a baseline for cybersecurity.
Why OWASP Top 10 Matters
Modern web applications are increasingly complex and interconnected, resulting in continuously emerging security vulnerabilities. The OWASP Top 10 supplies up-to-date insights into this evolving threat landscape, enabling organizations to understand and respond to the most critical risks they face.
OWASP Top 10 2021
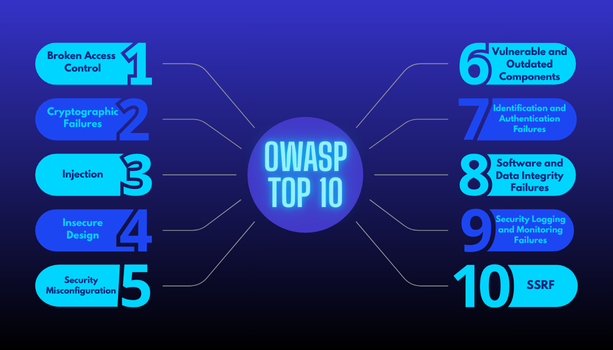
Reviewing OWASP Top 10 2021, changes between the 2017 and 2021 editions highlights OWASP’s sensitivity to the evolving threat environment. Given the rapid technological advancement and shifting attack methods from 2021 to 2025, significant changes in the 2025 list are highly anticipated.
Evolving Cyber Threat Landscape (2021–2025)

To forecast OWASP Top 10 2025, let’s examine the cybersecurity trends that are most likely to influence it:
A. Emergence of AI/ML‑Based Attacks and AI‑Native Vulnerabilities
Generative AI has rapidly become a new threat vector, with only 24% of AI‑using initiatives currently secured. Gartner predicts that 17% of cyberattacks will involve generative AI by 2027.
The OWASP Top 10 for LLM Applications 2025 prioritizes prompt injection (#1), sensitive data exposure (#2), and supply chain issues (#3) as AI‑specific critical vulnerabilities. Agent‑based AI systems introduce new API threats, especially in APAC, where 65% of AI agent project security issues are API‑related.
B. Rising Software Supply Chain Risks
Supply chain breaches have surged. Gartner forecasts that by 2025, 45% of global organizations will face software supply chain attacks; in 2024, 75% of software supply chains reported at least one attack. Incidents like the Kaseya ransomware (2021) and Okta social engineering (2023) underscore this trend. Consequently, the category “Vulnerable and Outdated Components” (A06:2021) will likely expand to encompass the entire software development and delivery pipeline, including CI/CD infrastructure and third‑party dependencies.
C. Persistent Cloud Security Issues and Misconfigurations
Cloud adoption continues to rise, but along with it, network complexity, misconfiguration risks, and vulnerable APIs. Gartner expects that by 2025, 99% of cloud security failures will be due to configuration errors from customer responsibility. Thus, “Security Misconfigurations” (A05:2021) may not only remain a top threat but grow increasingly significant.
D. Escalating API Security Vulnerabilities
APIs have become central in cloud‑native and AI workflows. Their role is amplified by AI agents and supply chain threats. In Q1 2025, prominent API vulnerabilities include poor access control, authentication flaws, and unsafe resource usage. This amplifies the relevance of categories like “Broken Access Control” (A01:2021), “Identification and Authentication Failures” (A07:2021), and “Security Misconfigurations” (A05:2021), especially in API‑specific contexts.
E. Emerging IoT Security Challenges
With an estimated 35.2 billion IoT devices globally in 2025, security remains a pressing concern. From 2024 to 2025, IoT malware infections increased by 27%. Among consumer IoT devices, 82% lack proper access control or password protection, and 75% use insecure protocols. Though not traditional web applications, IoT devices often serve as initial attack vectors leading to ransomware or critical infrastructure disruptions, directly contributing to “Identification and Authentication Failures” (A07:2021) and “Vulnerable and Outdated Components” (A06:2021).
F. Ongoing Dominance of Ransomware, Phishing, and Zero‑Day Exploits
These attacks are still very effective and often found to be main ways to attack vulnerabilities.
- Ransomware continues its upward trajectory, being responsible for 59% of cyberattacks in 2024; 32% were due to unpatched vulnerabilities, and incidents are projected to occur every 2 seconds by 2031.
- Phishing initiates 80 to 95% of human‑related breaches, increasingly enhanced by AI sophistication.
- Zero‑Day Exploits: 97 exploited in 2023 and 75 in 2024; in Q1 2025, over 25% of vulnerabilities were exploited within 24 hours of disclosure, highlighting accelerated threat propagation.
OWASP Top 10 Predictions for 2025
Broken Access Control
Access control failures remain the top cybersecurity risk across modern distributed architectures such as cloud environments, APIs, and IoT devices. Due to the fundamental nature of access control flaws, this category is expected to persist as a primary threat. The widespread distribution of resources in modern systems amplifies the prevalence and impact of these vulnerabilities.
Security Misconfigurations
In cloud environments in particular, security misconfigurations are a leading cause of breaches. Gartner forecasts that by 2025, 99% of cloud security failures will be due to customer misconfigurations. The dynamic and complex nature of cloud, API, and AI systems exacerbates this persistent human error issue.
Injection
Traditional injection vulnerabilities are still widespread, but new variants are emerging due to AI proliferation. Adversarial inputs and prompt injections can manipulate AI decision-making or extract sensitive data, compromising the integrity of AI models. These threats expand the classic injection category into the realm of AI systems.
Insecure Design
Although it was only recently introduced in the 2021 list, insecure design will gain further importance in 2025. The growing complexity of cloud-native and microservices architectures often results in insufficient security considerations during the design phase, leaving systems vulnerable by default.
Vulnerable and Outdated Components
This category is expected to elevate due to rise in software supply chain attacks. By 2025, an estimated 45% of organizations worldwide will experience software supply chain attacks. These attacks exploit outdated components and dependencies, posing a widespread and growing threat.
Identification and Authentication Failures
This risk becomes more prominent with the rise of AI-driven phishing and proliferation of IoT devices. Phishing attacks initiate 80–95% of all human-related breaches. AI can generate highly sophisticated and undetectable phishing attacks that bypass traditional authentication mechanisms, making this an increasingly critical concern.
Software and Data Integrity Failures
This category expands with the intersection of software supply chain vulnerabilities and AI interaction. Attacks may inject malicious payloads into software updates or compromise CI/CD pipelines. AI models are also susceptible to “data poisoning,” which undermines the integrity of training datasets.
Security Logging and Monitoring Failures
As attacks become more frequent and faster, traditional logging and monitoring systems are often insufficient. Automated attacks using AI-powered malware and IoT botnets highlight the urgent need for faster detection and response. Notably, attackers exploited over 25% of vulnerabilities in Q1 2025 within 24 hours of public disclosure.
API Security Risks
APIs have become universal entry points for a wide range of attacks. Existing web application security practices often fall short in addressing the unique characteristics of APIs. With APIs forming the backbone of modern applications, the industry is increasingly recognizing that “APIs are not just part of the attack surface—they are the attack surface.”
AI/ML System Vulnerabilities
AI is not only amplifying existing threats but also introducing entirely new attack surfaces and unique classes of vulnerabilities. Prompt injection, data poisoning, model inversion and extraction, and prompt leakage are just a few examples. The emergence of a separate OWASP Top 10 for LLMs reflects how these risks extend beyond the scope of traditional web application threats.
Global Cybersecurity Leadership: Penta Security
The 2025 OWASP Top 10 clearly shows that while the core principles of web application security remain relevant, the scope and focus are rapidly evolving. New complexities and attack vectors are being introduced by emerging technologies such as AI, cloud computing, APIs, and IoT. Persistent issues like “Broken Access Control” and “Security Misconfigurations” will only deepen in modern distributed environments. Meanwhile, “Vulnerable and Outdated Components” are becoming increasingly critical due to the systemic nature of supply chain attacks.
As a top global cybersecurity company, Penta Security has stayed ahead of these shifting dynamics for nearly three decades. Through trusted solutions like Intelligent Web Application and API Protection (WAPPLES), ALL THAT ENCRYPTION (D.AMO), and the Cloud Security SaaS Platform (Cloudbric), we have continually adapted to secure evolving IT infrastructures.
Equipped with both the advanced technology and hands-on experience needed to counter threats expanding through AI, cloud, and APIs, Penta Security serves as a reliable partner in helping organizations embrace digital transformation with confidence. With continuous R&D and real-world global expertise, Penta Security remains committed to delivering the most effective strategies for emerging cybersecurity threats.
Click here to subscribe our Newsletter
Check out Penta Security’s product lines:
Web Application Firewall: WAPPLES
Database Encryption: D.AMO
Click here for inquiries regarding the partner system of Penta Security
Check out the product lines of Cloudbric by Penta Security:
Cloud-based Fully Managed WAAP: Cloudbric WAF+
Agent based Zero Trust Network Access Solution: Cloudbric PAS
Agentless Zero Trust Network Access Solution: Cloudbric RAS
Click here for inquiries regarding the partner system of Cloudbric